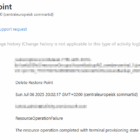
Recently, I tried to configure Veeam Backup and Replication for Azure. When trying to let Veeam configure the Azure app and its privileges automatically, it failed (probably due to some MFA requirment or other restrictions in the Azure environment), Instead, I tried to create the Azure app manually, and assigning all the required privileges on my own, but always ended up with errors like “No Microsoft Azure subscriptions found” and “Failed to create an account: One or more errors occurred”.
After reading through a lot of documentation, both from Veeam and Microsoft, I managed to create an Azure app and assigning it the right set of privileges.
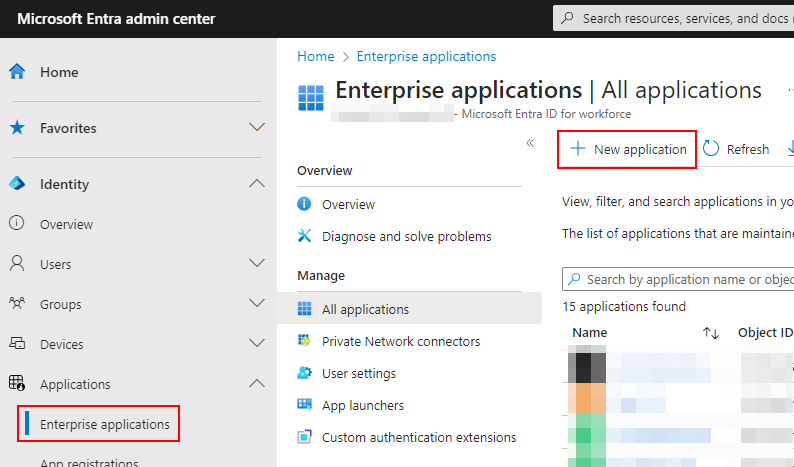
In Entra ID (https://entra.microsoft.com), sign in with an admin account and go to Applications, Enterprise applications, and New application.
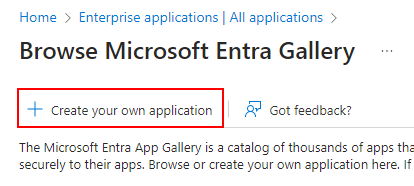
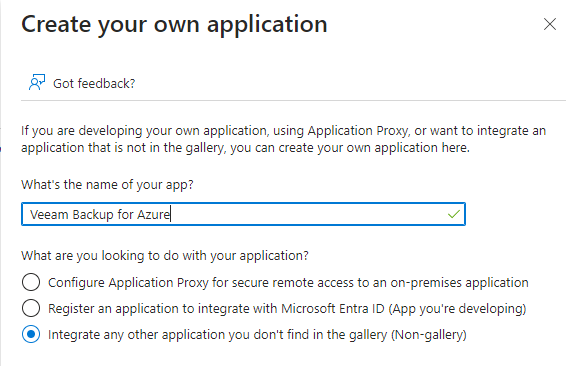
Click on Create your own application, give it a name (e.g., Veeam Backup for Azure), make sure Non-gallery is selected, and click on Create.
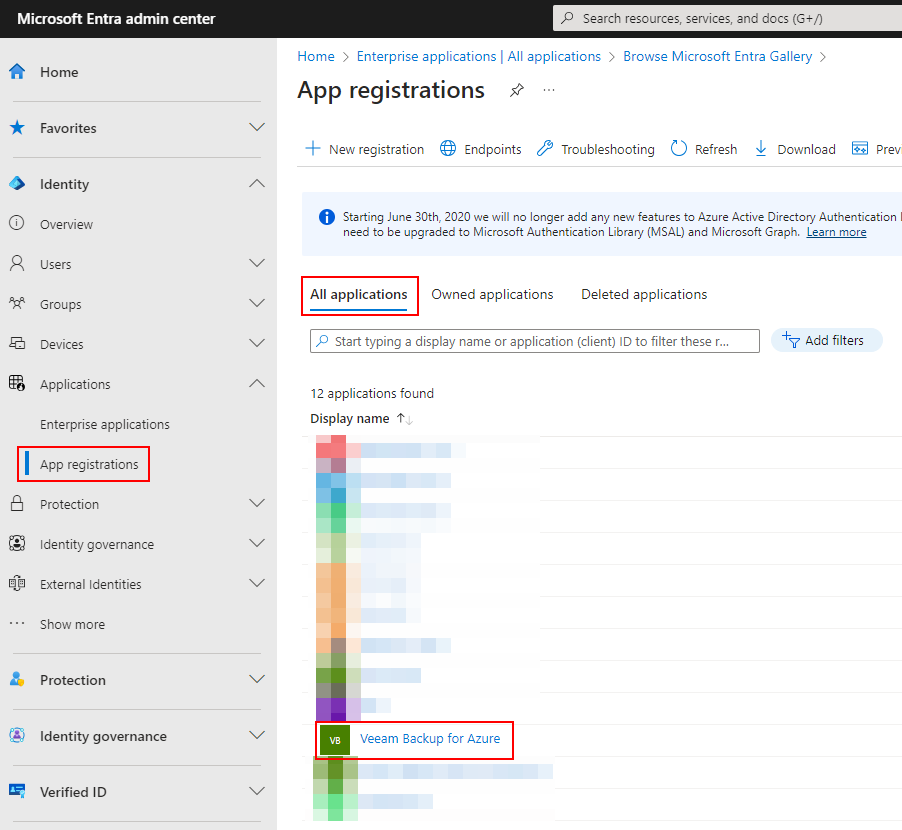
Now, go back to the Entra ID portal, go to Applications, App registrations, All applications, and open your newly created app.
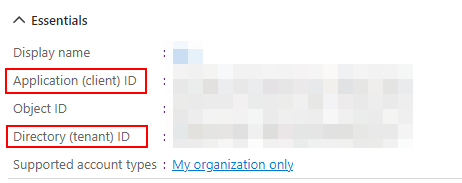
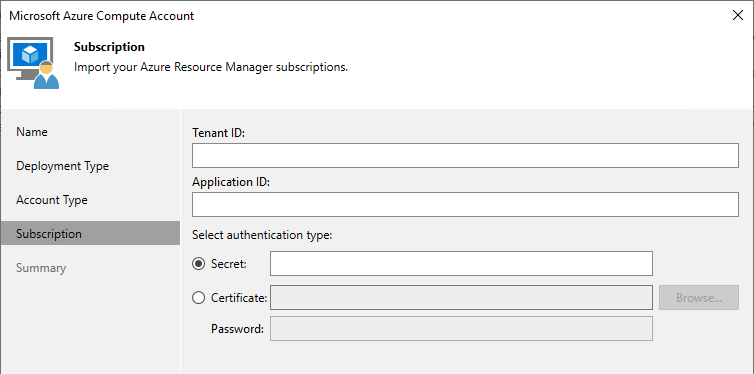
Note the Application (client) ID and the Directory (tenant) ID. Those will be needed later.
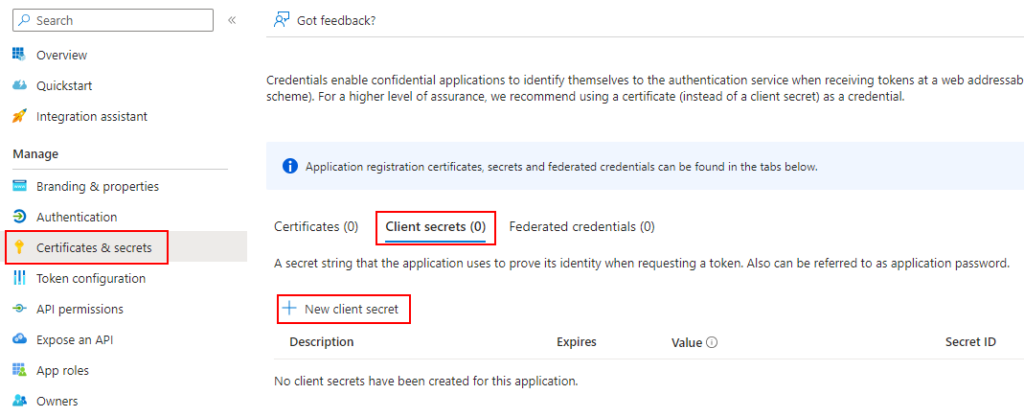
Continue to Certificates & Secrets, Client secrets, and click on New client secret.
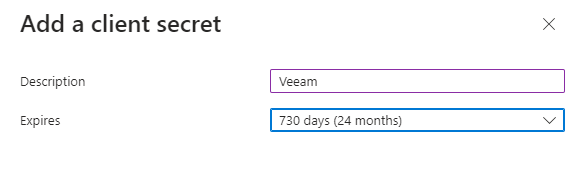
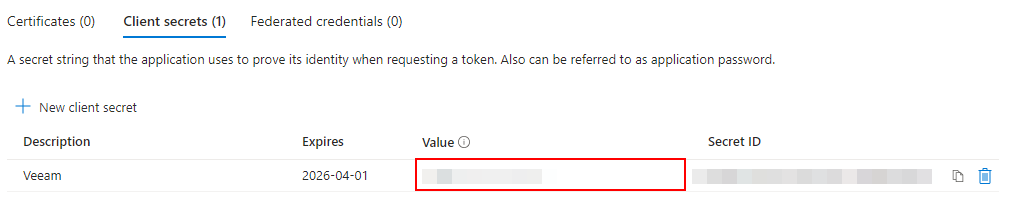
Enter a description (e.g., Veeam), select an approperiate validation period, click on Add, and note the secret’s Value. This will be needed later.
So far no problem. This is rather a standard approach when creating an app. Now the tricky part. Normally, you would add some API permissions for the application, but for Veeam, built-in Azure roles must be added to the application. Roles (e.g., Owner) are something you usually assigns to a user.
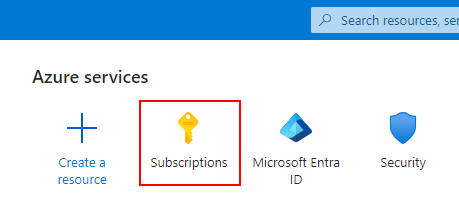
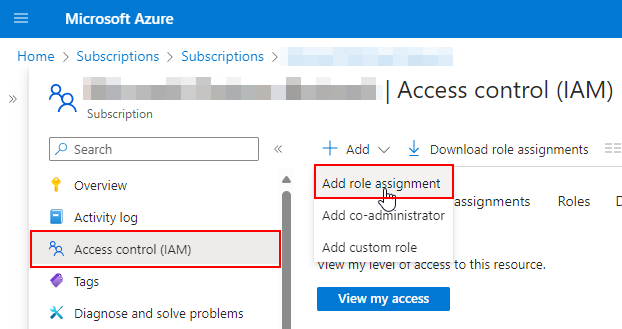
Now, in the Azure Portal (https://portal.azure.com), go to Subscriptions, open your subscription, click on Access control (IAM), Add, and Add role assignment.
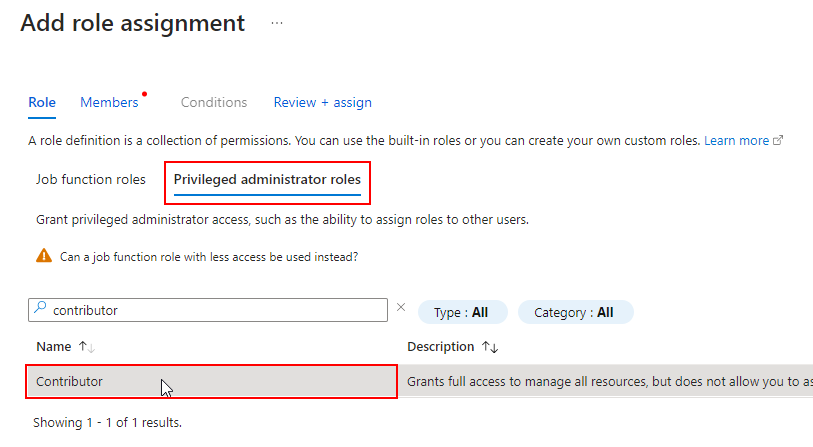
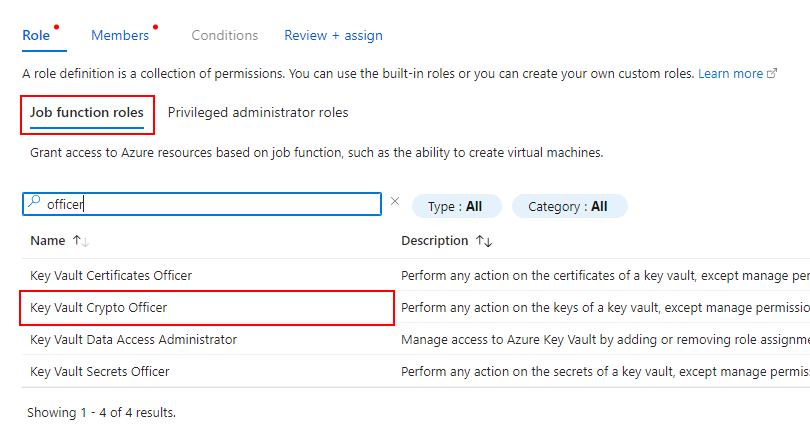
According to Veeams documentation, Contributor and Key Vault Crypto Officer roles are needed. Start with the Contributor role on the Privileged administrator roles tab.
Now the tricky part. As said earlier, roles are normally only assigned to users. Go to the Members tab and click on Select members.
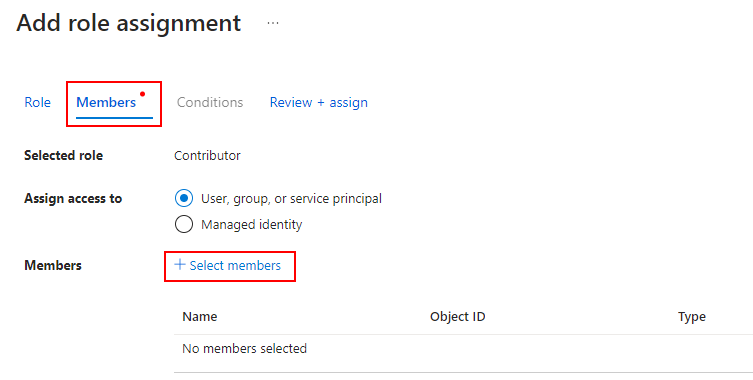
Only users and groups are selectable.
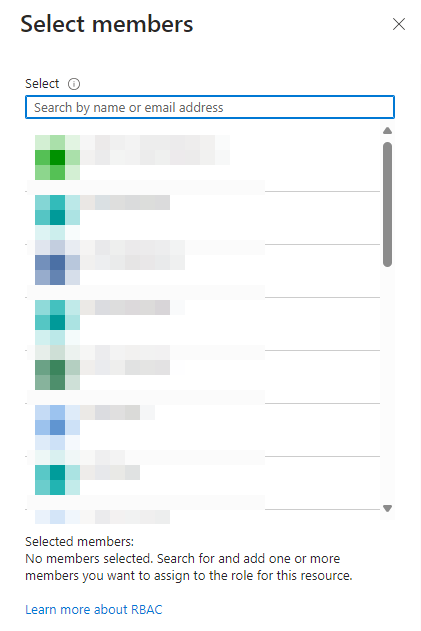
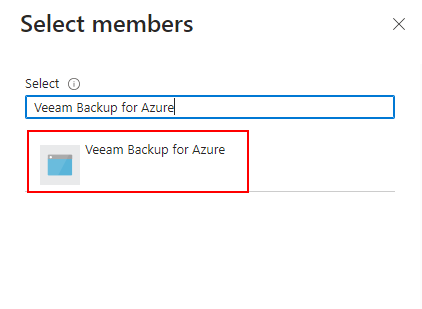
This is where I got lost, but apparently all you need to do is search for the application created earlier (e.g., Veeam Backup for Azure).
Now do the same but for Key Vault Crypto Officer under the Job function roles tab.
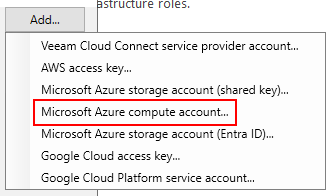
Now over to Veeam and add your app’s credentials (Credentials & Password -> Add -> Microsoft Azure compute account).

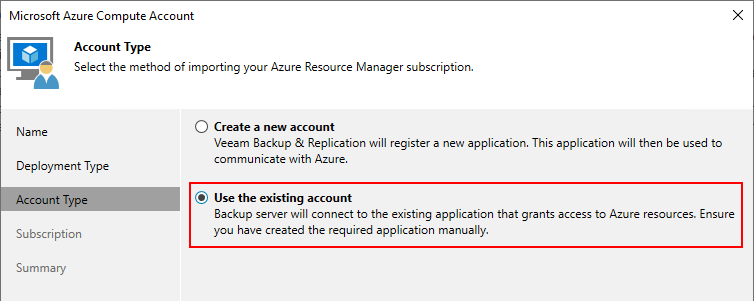
Choose Use the existing account.
Enter the information noted earlier and click on Next.
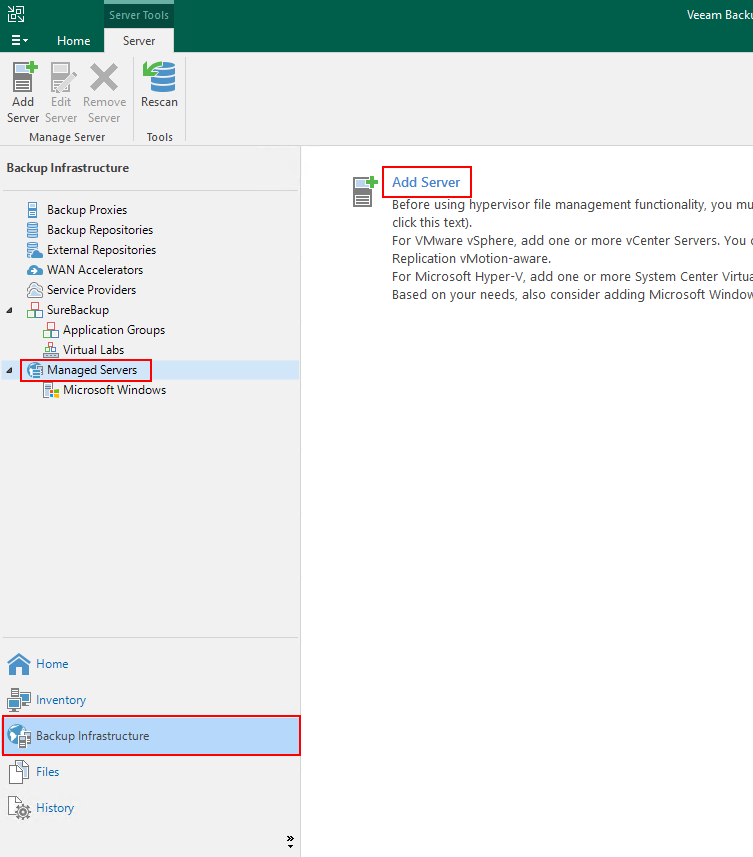
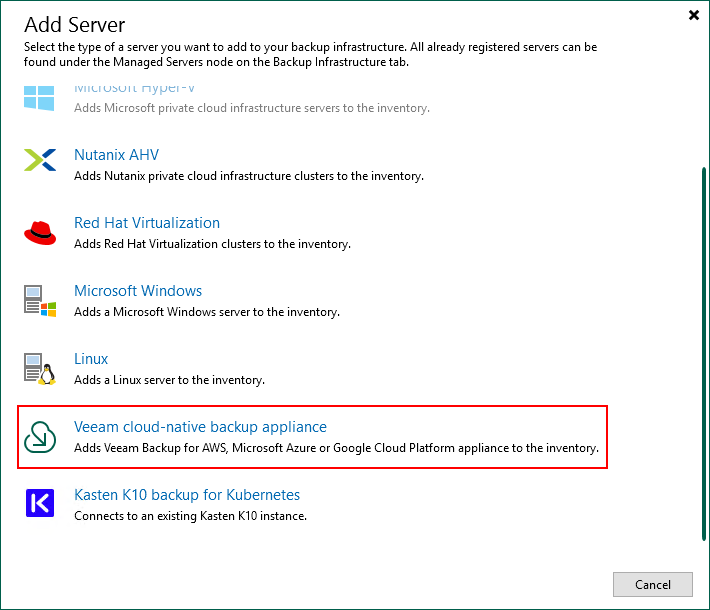
You should now be able to proceed adding your Azure infrastructure to Veeam. In my case, I do everything manual – even creating the backup applicance. Under Backup Infrastructure and Managed Servers, click on Add Server and select Veeam cloud-native backup appliance and Veeam Backup for Microsoft Azure.
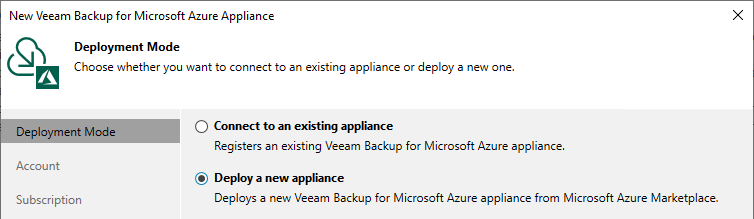
Choose to Depoloy a new applicance and click on Next.
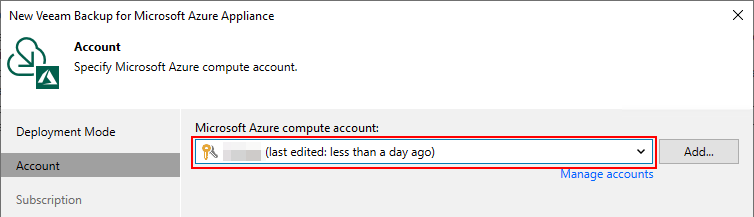
Select your newly created cloud credentials and click on Next again.
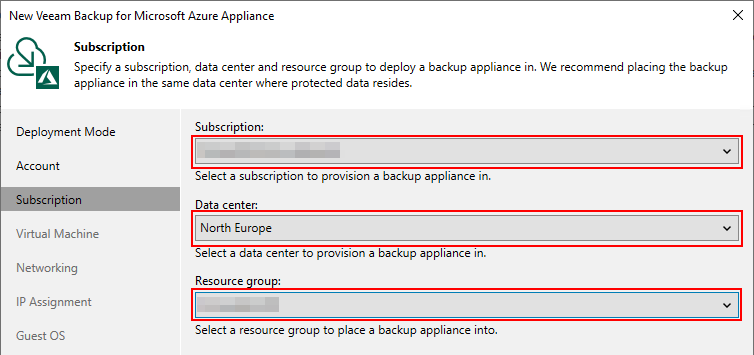
Now you should be able to select your subscription, data center location, resource group, and continuing deploying your backup appliance.